This article describes the main concepts of SQL injections, analyzes the most popular types of vulnerabilities and also, provides information on the best ways to prevent SQL code entering into a website.
The main reasons for using SQL injections
The main vulnerabilities of applying SQL injections appear when the group of information managed by a user requests connection to a database in an unsafe mode.A hacker can easily create a specially developed input, to extract data from context, in which they are displayed, and instantly intrude into the structure of the necessary request.
The process of applying SQL injection can be followed by several sequences of malicious attacks, including hidden reading or editing crucial parts of information, unauthorized interference with the logic of application’s functioning, increasing the user privileges in a database, and even complete control of a certain database server.
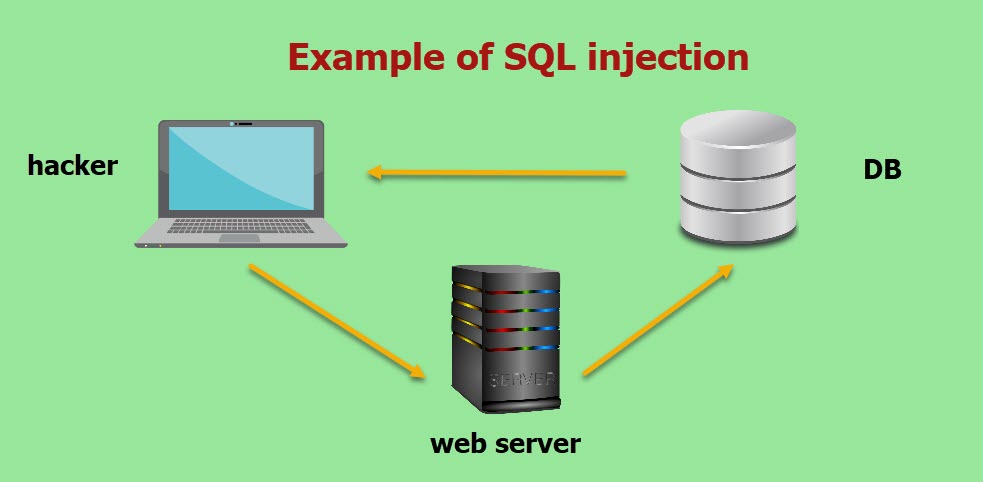
Example of SQL Injection
The most common examples of using SQL injections:
- Possibility to receive personal access to the hidden data where you can easily apply SQL query, to receive additional information;
- Breaking the logic of the application’s functioning, where the request is being edited, so that the application can’t work according to common and primarily established logic;
- Executing the UNION attacks, that give the possibility to receive information from various DB tables;
- Learning the databases that can be used for extracting the information on the database’s version and its type;
- Blind usage of SQL injections when the result of a request doesn’t return in software responses.
We can understand the nature of SQL injections on the basis of the UNION attack.
Such a type of attack can be applied in the cases when the results of a SQL query return in the application’s responses.A hacker can easily get additional information from other tables inside the database, by using SQL injections.
UNION operator helps a user to successfully build an additional SELECT request and rapidly add the results to the body of an initial query.
For example, the software executes the request for accessing the information on current discount offers in the “Gifts” section.
SELECT name, description FROM products WHERE category = ‘Gifts’
A hacker can easily add an additional request to get the client’s data:
‘UNION SELECT username, password FROM users–
The server of the application that is being attacked accepts the request to process data and sends the following formulated request to the database:
SELECT name, description FROM products WHERE category = ‘Gifts’ UNION SELECT username, password FROM users–
As a result, a hacker will get access not only to a name but also to complete product description, and also, he/she will get all information regarding names and passwords of the website users or web app users.What are the methods to test software for SQL injections?
Most SQL vulnerabilities can be easily found with the help of various scanners of web vulnerabilities (in a modern IT community, OWASP, and Burp Suite are very popular).
SQL usage can be also found by using systematic test suites for every application input.
Such actions commonly include the following steps:
- the possibility to send the symbols of a singular “ mark and to search for errors or other anomalies;
- the possibility to send a certain group of syntaxes, specific for SQL, that can evaluate primary values of input and search for systematic differences in the software requests that have been received;
- operating logical conditions such as OR1 = 1 and OR1 = 2, and finding various results in software requests;
- sending useful information that is primarily aimed at launching temporary time-outs inside SQL body and finding various differences in the amount of time, needed for getting the response.
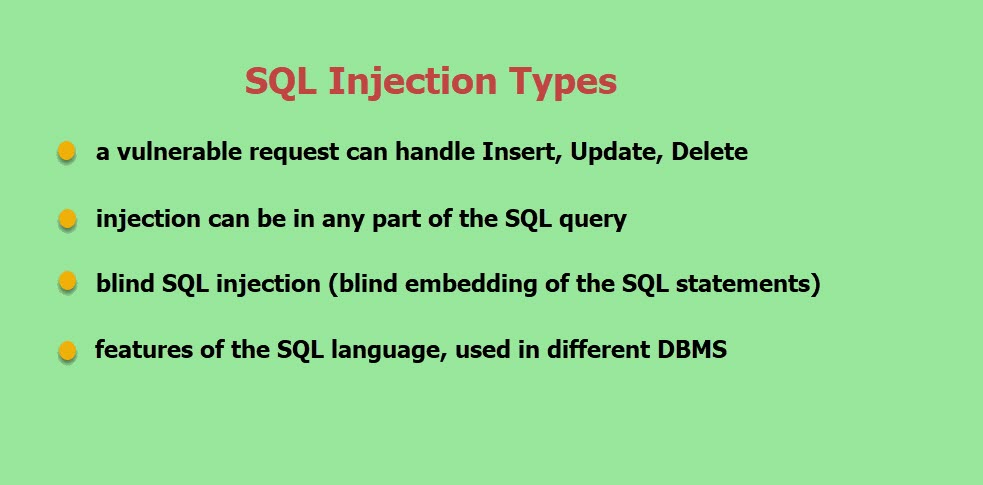
SQL Injection Types
Different ways to protect yourself from unauthorized SQL injections
To not meet such problems while releasing the software, you should follow very simple but working rules.
You just need to constantly monitor data inside the request with the help of a simple handler. You should also separate information from commands and requests.You can use one of the following methods for doing this:
- Using secure API that allows excluding interpreter usage and which offers a complete parameterized interface. You can also use ORM (Object-Relational Mapping) tools;
- Implementing white lists in the server, with the necessity to check all incoming data. Obviously, such a method can’t provide a client with complete safety since several applications can easily use various special symbols (for example, inside text fields or for needs of API inside a mobile application);
- Possibility to imply shielding of special symbols for other dynamic requests, by using the syntax that is suitable for the interpreter. Note: all elements of SQL architecture, namely names of tables or columns can’t be shielded, therefore, names that you give the clients can be unsafe, in some way. It’s a very popular problem for all platforms that provide the possibility to generate information reports.
- Using elements of controlling SQL inside a request body, to potentially prevent the information leakages.
Instead of conclusion
Of course, there are no absolutely safe systems, you just need to decrease the possibility of potential hacking.
To prevent malicious SQL injections, you need to thoroughly test the parameters received from a client with the help of any available methods.You can try to break a website yourself before it is released, to know for sure what system vulnerabilities it can have: enter injection, edit a request type, add several special symbols to shielding fields, try to upload the documents with malicious code to a website file repository, etc. (perform complete security testing services).
And remember: it’s better to spend some time that you and a developer have for searching for vulnerabilities than to fix the things that an attacker has done.










Leave A Comment